What ALL SMBs and Solopreneurs must know!
When it comes to headlines in cybersecurity, it's often the large companies that receive the most attention. However, the reality is that small businesses are actually more frequently targeted by cyberattacks. In fact, a staggering 43% of all data breaches are directed at small businesses.
Complacency is NOT an option!

Alarming CyberSecurity Statistics
- It takes at least a half a year to detect a data breach
- At least 43% of Cyber Attacks target SMBs
- 91% of cyber-attacks begin with a phishing email
- A business falls victim to ransomware every 11 seconds
- 38% of malicious attachments are disguised as Microsoft Office files
- The CyberSecurity market is expected to reach $300 BILLION by 2024
All size businesses, including SMBs, in all industries are at risk for cyber-attacks, resulting in lost income and possible lawsuits.
Laws are expanding on a daily basis in terms of the data that businesses are legally expected to protect. This includes your company's data and any customer information on your network.
Every minute normal business operations are forced to stop is a loss of income. Depending on the length of time this interruption causes, a business is at risk of losing significant income. The business may also be found liable for any damages that result from an attack.
Many SMBs cannot recover from a Cyber-attack.
Are SMB's more vulnerable to cybercriminals? YES!
WHY?
- Small or no IT/Security staff and infrastructure
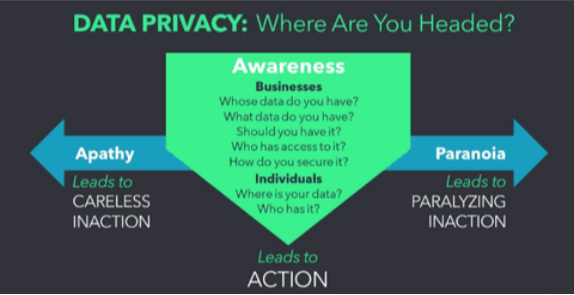
- Lack of awareness or knowledge about how to protect themselves and/or their business
- False sense of security (e.g., "criminals only target huge companies")
- Belief they cannot afford to implement the same robust safety measures as larger companies
- Use off the shelf and/or multiple security sources creating vulnerability gaps
Off the shelf CyberSecurity products are all I need, right? NO!
WHY?
- CyberSecurity criminals know these solutions have a lot of gaps actually leaving companies vulnerable. They simply can't protect businesses at the same level as CAT's top-tier Proactive CyberSecurity solutions
- 400,000 to 450,000 new malware variants are detected every day. There are now more than 1 billion malware programs out there. Every minute, four companies fall victim to ransomware attacks.
-
Many of today's most crippling cyberattacks come from these new threats which are being created every day. The only way to guard against these unknown variables is to deploy a solution that is constantly (24 x 7) on the lookout for these unknown variables.
CAT is constantly monitoring and collecting threat intelligence info from around the globe to provide automatic updates to all our clients within minutes. CAT's solutions are customized and automated.

SMB's Must Become Proactive!
If your small or medium-sized business (SMB) experiences a compromise of either your customers' or clients' social security numbers or personal identities, the repercussions can be severe. Cybercriminals could exploit this data to initiate activities such as opening unauthorized credit accounts, obtaining loans, or submitting fraudulent tax returns on behalf of your business associates. The outcome may involve financial losses, harm to your business's credit standing, and a significant amount of stress and frustration.
While monitoring services can help you detect fraudulent activity after it has occurred, (Reactive) it is important to note that they cannot prevent the damage from happening in the first place.
As an innovative cybersecurity provider, we proudly offer one of the only comprehensive and affordable 24/7 protection packages designed specifically for small and medium-sized businesses (SMBs). Our unique solution encompasses continuous monitoring and essential employee cybersecurity training, providing an unmatched level of security. Acknowledging the inherent challenge of achieving 100% protection, our commitment is to deliver top-notch defense, significantly reducing the risk of breaches for SMBs.
What is Malware?
Malware is short for "malicious software". Malware is designed to damage and destroy computers and computer systems.
Malware is particularly damaging for SMBs because it can cripple devices, which require expensive repairs or replacements. Malware can also provide a back door to access data, which potentially puts customers and employees at risk.
SMBs generally contract with people or 3rd parties who use their own devices for work saving time and cost. However, this increases the likelihood of a malware attack, as personal devices are much more likely to be at risk from malicious downloads.

Trojan horses, viruses, spyware, adware, ransomware ... some of these have fancy names, others just sound ominous. However, there is one thing they all have in common:
You don't want any of these anywhere near your computer, smartphone, or tablet! (Devices)

What is Malware?
Malware is short for "malicious software". Malware is designed to damage and destroy computers and computer systems.
Malware is particularly damaging for SMBs because it can cripple devices, which require expensive repairs or replacements. Malware can also provide a back door to access data, which potentially puts customers and employees at risk.
SMBs generally contract with people or 3rd parties who use their own devices for work saving time and cost. However, this increases the likelihood of a malware attack, as personal devices are much more likely to be at risk from malicious downloads.
SMB's can no longer afford to wait when it comes to CyberSecurity!
Don't settle for delayed action in CyberSecurity. While others promise 24/7 monitoring, they often lack proactive responses. At CAT, we deliver instant incident response and Fortune 100 level protection affordably. Our experts swiftly detect, analyze, and respond to threats in real-time, ensuring no delays, no overlooked alerts.
Experience peace of mind knowing CAT provides
Proactive CyberSecurity, 24/7, at an affordable price.
Phishing Attacks
The most damaging and most widespread threat facing SMB's is Phishing Attacks. Phishing Attacks account for 90% of all breaches. This continues to grow and has represented billions of dollars is losses.
A Phishing Attack occurs when a user is enticed to click a malicious link, download a malicious file, or give the hacker access to sensitive information, account details or credentials because the request appears legitimate.
People trust emails coming from reputable brands and tend to click or open these emails.

Phishing emails are fraudulent emails that are designed to trick people into giving away their personal information. Cybercriminals use a variety of tactics to make these emails look legitimate, including using subject lines that are designed to grab the recipient’s attention.
According to a study by cybersecurity company Barracuda Networks, some of the most common phishing email subject lines according to zdnet.com include:
1. Request: This is the most common subject line used in phishing emails, accounting for over a third of all phishing messages analyzed.
2. Follow up: This subject line is often used to create a sense of urgency and pressure the recipient into taking action.
3. Urgent/Important: This subject line is also used to create a sense of urgency and pressure the recipient into taking action.
4. Are you available? / Are you at your desk? This subject line is often used to trick the recipient into thinking that the email is coming from a colleague or boss.
5. Payment Status: This subject line is often used to trick the recipient into thinking that there is an issue with their payment.
Additional Popular Email Subject Lines:
- DocuSign: Please review and sign your document
- Equipment and Software Update
- Mail Notification: You have 5 Encrypted Messages
- Google: Password Expiration Notice
- Action Required: Your payment was declined
- Package Delivery Failed - Click to Reschedule
- Important Tax Refund Notification
- Your Subscription Has Expired - Renew Now!
- Urgent: Verify Your Banking Details
CATCyberSecurity's Philosophy is to
Prevent vs. React!
CAT operates behind the scenes to protect businesses by managing threats before they get in. This saves our clients time and thousands of dollars dealing with costly problems associated with simply reacting to threats and data breaches after they occur.
 CATCyberSecurity
CATCyberSecurity
a division of Cloud Advantage Technologies, LLC
Sales: 800-228-5709
Hours Weekdays: 9am - 5pm, Saturday 10 am - 2 pm
Email: [email protected]
Email: [email protected]
Email: [email protected]
Email: [email protected]
Email: [email protected]

